Machine-Speed Infiltration: A Detailed Analysis of AI-Driven Fortigate Exploitation
The Era of the Automated Exploit
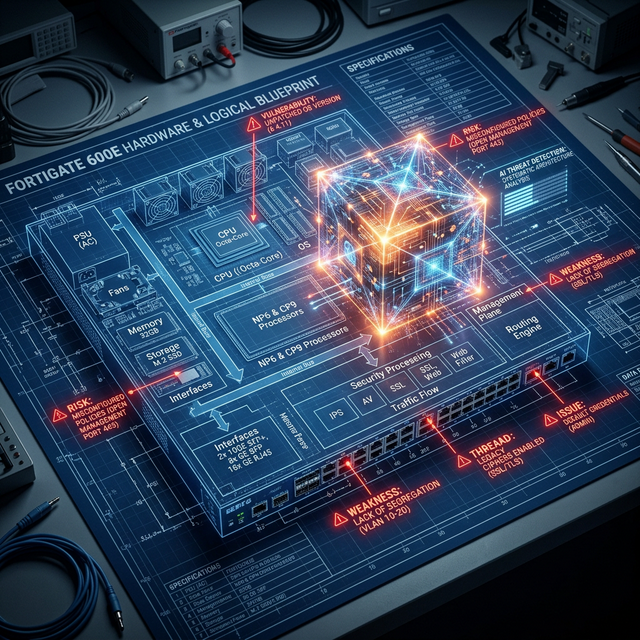
Recent telemetry has revealed a new and disturbing trend in the cyber battlefield: AI-Driven Exploitation. In a coordinated campaign targeting Fortigate SSL-VPN devices, threat actors used an autonomous AI framework to scan the internet, identify vulnerable targets, and deploy complex exploits in a fraction of the time a human team would require. We are no longer defending against scripts; we are defending against an evolving intelligence.
The human defender is officially becoming the bottleneck in cybersecurity.
The AI Infiltration Workflow
The AI system doesn't just "fire and forget." It follows a sophisticated, adaptive workflow that mimics an elite human red team:
Rapid Reconnaissance
The system uses massively distributed infrastructure to "fingerprint" every Fortigate device connected to the internet. While a manual scan would take days, the AI completes this phase in minutes, creating a real-time map of the global "attack surface."
Autonomous Payload Generation
When the AI identifies a target, it doesn't just use a generic script. It analyzes the target's firmware version and network configuration to generate a custom obfuscated payload on the fly. This payload is specifically designed to bypass the local Antivirus and Intrusion Prevention Systems (IPS).
Machine-Learning Evasion
If the exploit fails, the AI doesn't quit. It analyzes the failure logs, "learns" why it was blocked, and immediately tries a different technique. It iterates through thousands of variations until it finds the "one key" that turns the lock.
Defending at the Speed of AI
To survive an autonomous attack, your defense must be just as fast and just as intelligent. Here is the Grivyonx approach to AI-ready security:
- Automated Threat Response (SOAR): We help you implement systems that can "unplug" a compromised device or update a firewall rule automatically in milliseconds. If you wait for a human to see the alert, the AI has already won.
- Zero-Trust Perimeter: Treat every incoming connection as potentially malicious. We help you move beyond "edge security" to a model where every internal resource is individually protected.
- Edge Intelligence: Use security appliances that perform real-time behavioral analysis at the packet level to identify the "rhythm" of an AI-driven scan.
The Grivyonx View
At Grivyonx Cloud, we are pioneers in Hyper-Speed Security. We build the "Digital Shields" that protect our clients from the "AI Swords" of the future. We provide the automation, the expertise, and the intelligence to ensure you stay ahead of the machines. The speed of attack is accelerating. Is your defense? Let's talk about automated resilience.

Gourav Rajput
Founder of Grivyonx Technologies at Grivyonx Technologies
Deep Technical Content


